In the world of software development, staging environments are useful, but they lie to you. They use fake data that often looks nothing like the chaotic, messy reality of production. In 2026, the standard for Indian tech giants (from Bengaluru to Gurugram) has shifted to a safer, smarter method: Mirror Testing, also known as Shadow Traffic.
If you are a backend engineer or a system architect worried about breaking things during a migration, this guide is for you. We will break down what mirror testing is, how it works, and how you can implement it to deploy with zero stress.
Table of Contents
Key Takeaways
- Definition: Mirror testing safely validates code by copying live traffic to a new version without impacting end users.
- Safety First: Always implement “Dry Run” logic to prevent shadow services from writing to databases or triggering side effects.
- Tools: Use native features in Istio (for Kubernetes) or NGINX (for VMs/dedicated servers) to enable mirroring with one line of config.
- Privacy Compliance: Apply data masking to mirrored requests to protect user PII and comply with legal standards.
What is Mirror Testing (Shadow Traffic)?
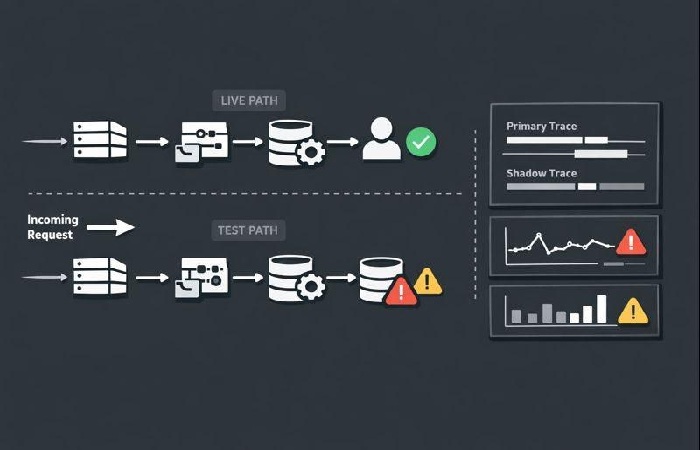
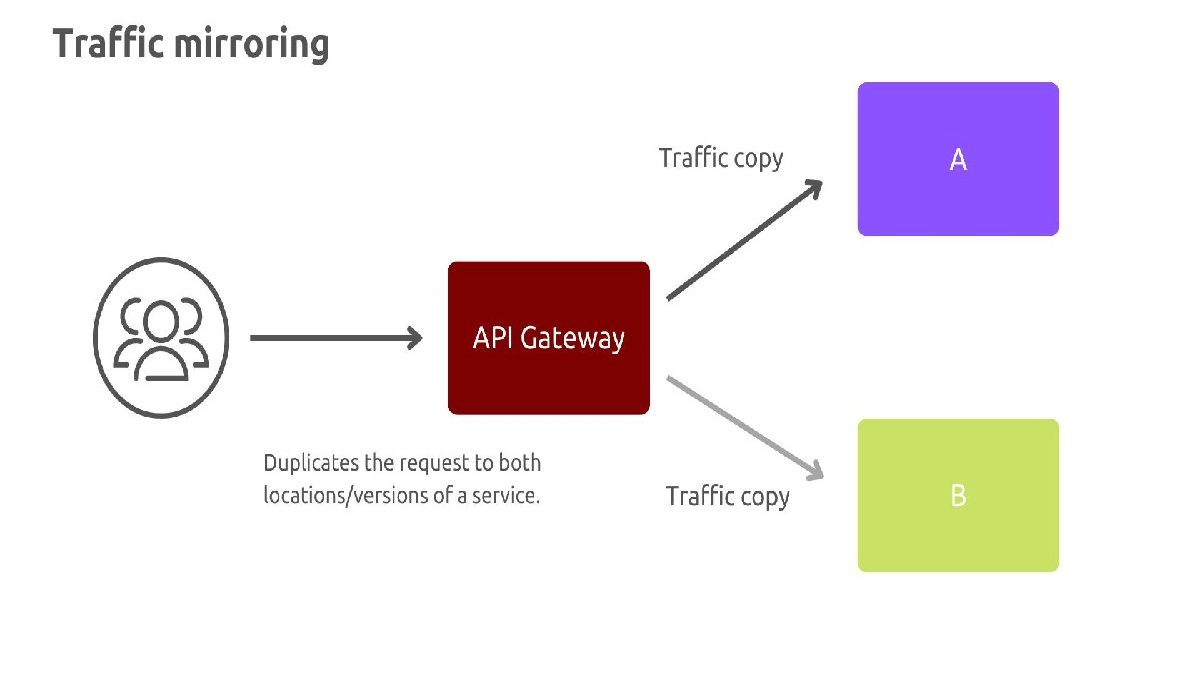
Mirror testing is a technique where live production traffic is copied (or “mirrored”) and sent to a new or updated version of your service. The critical rule is that the response from the mirrored version is ignored. The user only ever interacts with the stable, old version.
Think of it as a rehearsal. The new actor (your code) performs the play live in front of an empty theatre, while the audience only sees the star actor. You get to see exactly how the new code behaves under real load without anyone complaining if it forgets its lines.
Who This Is For (And Who Should Avoid It)
This is for:
-
Fintech & Payment Companies: You cannot afford downtime. Mirroring lets you test payment processing logic without actually charging customers.
-
High-Traffic E-commerce Sites: Testing during the sale season requires real user behavior, not synthetic bots.
-
Teams Migrating Monoliths to Microservices: You need to know if your new Go or Java service behaves exactly like the old one.
Avoid if:
-
You are running a batch processing job (e.g., Friday night data cleanup) – mirroring is for request/response APIs.
-
Your database cannot handle double the writes (remember, you are cloning requests!).
-
You haven’t set up data masking (you risk leaking user emails to test environments).
Why “Shift Right” Beats Staging in 2026
The old way of testing (Shift Left) happens early, using synthetic data. But real users do unpredictable things. They send weird Unicode characters, they click buttons out of order, and they have specific session states.
Mirror testing represents Shift Right—moving testing closer to production. It answers the question: “Will this code survive Tuesday at 8 PM?” before you actually release it.
How to Implement Mirror Testing (Step-by-Step)
You don’t need expensive software to do this. If you are using Kubernetes or a modern proxy, you likely have the tools already.
The Simplest Setup: NGINX
If you use NGINX as your gateway, you can use the mirror directive.
server { location / { # Send request to the actual production server proxy_pass http://my-app-v1; # Send a copy to the new server for testing mirror /mirror; } location = /mirror { internal; # Users cannot call this directly proxy_pass http://my-app-v2; proxy_set_header X-Mirrored "true"; # Tell the new app it's a test } }
In this setup, the user waits for V1. V2 processes the data in the background.
The Service Mesh Approach (Istio)
For Kubernetes users, Istio makes this a configuration change, not a code change.
apiVersion: networking.istio.io/v1beta1 kind: VirtualService metadata: name: payment-service spec: hosts: - payment http: - route: - destination: host: payment-v1 # Stable version mirror: host: payment-v2 # Shadow version mirrorPercentage: value: 25.0 # Only mirror 25% of traffic to save resources
The “Golden Rule” of Mirroring: Handle Side Effects
The biggest mistake engineers make is letting the shadow service actually do things. If your service sends an email or deducts money, you cannot mirror that.
How to block this:
-
Header Detection: In your application code (V2), check for a header like
X-Mirror: trueorX-Shadow: true. -
The Switch: If the header is present, do not call the payment gateway. Do not write to the primary database. Only log the result or write to a test table.
Real-world example: A leading Indian BNPL provider uses mirror testing to validate their credit scoring models. They run the new model on live traffic but discard the decision—they only compare if the new score matches the old one before going live.
Data Privacy: The Non-Negotiable Rule
Under Indian IT rules and global standards like GDPR, you cannot copy user PII (Aadhaar, PAN, Email, Phone) to an unsecured testing environment.
The Solution: Data Masking
You must scrub the data before it hits the shadow service.
-
Strategy A (Proxy Level): Use Lua scripts in NGINX or filters in Istio to overwrite the
Authorizationheader or email fields with fake data. -
Strategy B (App Level): Your V2 code runs a “Dry Mode” where it reads the request structure but sanitizes the string values before processing.
Benefits vs. Drawbacks
| Benefits | Drawbacks |
|---|---|
| Real Data: Tests with actual user behavior, not mocks. | Resource Heavy: You need double the server capacity (V1 + V2). |
| Zero User Impact: Bugs in the new code cannot crash the user experience. | Complexity: Debugging can be tricky because logs are split across two systems. |
| Performance Benchmarking: Compare latency of V2 vs V1 under identical conditions. | Side Effects: Dangerous if you forget to disable write operations. |
Common Mistakes (And How To Avoid Them)
Mistake #1: Mirroring Database Writes
-
Symptom: Duplicate orders or corrupted data.
-
Fix: Implement
DEAD_CODEflags in your ORM layer to skip writes if theX-Mirrorheader is true.
Mistake #2: Ignoring the “Cold Cache” problem
-
Symptom: V2 is 10x slower than V1 because V1 has a hot cache (Redis/Memcached) and V2 doesn’t.
-
Fix: You might need to pre-warm V2, or ignore latency metrics for the first few minutes of testing.
Mistake #3: Mirroring 100% of Traffic
-
Risk: You might overwhelm your shadow cluster.
-
Fix: Start with 1% to 10% mirroring. You don’t need volume to find logic errors; you just need variety.
Real-World Scenario: Migrating a Checkout API
Imagine your team is rewriting a legacy PHP checkout service in Go.
Without Mirror Testing: You put the Go service live for 1% of users. If it has a bug, 1% of your customers cannot pay. You lose revenue.
With Mirror Testing: You deploy the Go service as a “Shadow.” It processes 100% of requests. You compare the Go response (silently) to the PHP response (sent to user).
-
Result: If Go returns a “500 error” for a specific cart state, you fix it before a single user ever sees it.
Conclusion
Mirror testing is the bridge between “it works on my machine” and “it works for our users.” In the high-stakes environment of Indian fintech and e-commerce, where a 5-minute downtime costs crores, this is not a luxury—it’s a necessity.
By starting with a simple NGINX mirror rule and adding strict data masking, you can move from hoping your code works to knowing it works.
Your Next Step: Try setting up a 5% mirror rule for a low-risk endpoint this week. Watch the logs. You will find a bug you didn’t know you had.
Frequently Asked Questions (FAQs)
Q: Does mirror testing slow down my website?
A: No. Mirrored requests are sent asynchronously or in a “fire-and-forget” manner. The user’s request waits only for the primary server (V1). The shadow server (V2) runs in the background without blocking the user.
Q: Is mirror testing the same as Canary deployment?
A: No. Canary sends real user traffic to the new version (risky). Mirroring sends a copy of the traffic to the new version (no risk). Mirroring is usually done before Canary.
Q: Can I mirror gRPC traffic?
A: Yes. Envoy proxy (used by Istio) natively supports mirroring for gRPC services.
Q: How do I handle authentication tokens (JWT) in mirrored traffic?
A: You should strip or replace them. If your V2 tries to validate a JWT for user “Bob” but Bob doesn’t exist in the shadow DB, it will fail. Use middleware to replace the JWT with a generic service account token.
Wikipedia Reference: